Approx. read time: 9.8 min.
Post: Dharma Ransomware Uses Legit Antivirus Tool To Distract Victims
Dharma ransomware, also known as CrySiS, is a notorious strain of ransomware first identified in 2016. It has evolved significantly over the years, maintaining its presence through continuous updates and variations.
Key Characteristics
- Ransomware-as-a-Service (RaaS): Dharma operates as a service, allowing cybercriminals to use its infrastructure to carry out attacks in exchange for a share of the ransom profits (Acronis) (Broadcom Inc. | Connecting Everything).
- Delivery Method: The primary method of infection is through Remote Desktop Protocol (RDP) connections. Attackers exploit weak or leaked credentials to gain access to systems (Acronis) (Broadcom Inc. | Connecting Everything).
- Encryption: Once it infects a system, Dharma encrypts files using a combination of AES-128 for data and RSA-1024 for the encryption key. It targets a wide range of file extensions and adds a specific suffix to each encrypted file (Acronis) (Cymulate).
Infection Process
- Initial Access: Attackers manually deploy Dharma via compromised RDP sessions.
- Persistence: The malware disables file system redirection and copies itself to various startup locations to ensure it runs on system boot. It also modifies registry keys to achieve persistence (Acronis) (Broadcom Inc. | Connecting Everything).
- Encryption: Dharma terminates various database services and processes to unlock and encrypt files. It deletes shadow copies using the
vssadmincommand to prevent victims from recovering their data easily (Broadcom Inc. | Connecting Everything) (Cymulate). - Ransom Note: After encryption, it drops a ransom note on the victim’s system, demanding payment for the decryption key. The note usually includes instructions for contacting the attackers and making the payment (Cymulate).
Prevention and Mitigation
- Strengthen RDP Security: Disable RDP if not needed or secure it with strong, unique passwords and multi-factor authentication.
- Regular Backups: Maintain regular backups and store them offline to ensure data can be restored without paying the ransom.
- Endpoint Protection: Use advanced endpoint protection solutions that can detect and block ransomware activities.
Recovery
Decryptor tools have been released for some variants of Dharma, allowing victims to recover their files without paying the ransom. However, the effectiveness of these tools can vary depending on the specific strain of Dharma involved (Acronis) (Broadcom Inc. | Connecting Everything).
For a deeper dive into the technical details and attack vectors of Dharma ransomware, you can refer to Acronis, Broadcom, and Cymulate articles.
Dharma Ransomware Uses Legit Antivirus Tool to Distract Victims
A new Dharma ransomware strain utilizes ESET AV Remover installations to distract victims while encrypting their files. Trend Micro detailed this “smoke screen” technique in a recent analysis.
Infection Method
Attackers push the ransomware through a spam campaign. The campaign delivers email attachments containing a Dharma dropper binary. This binary is packed as a password-protected self-extracting archive named Defender.exe, hosted on the compromised server link[.]fivetier[.]com.
Infection Chain
The spam email provides the password for the malicious attachment, encouraging curious victims to open the archive and inadvertently launch the Dharma-infected executable.
Spam Email Contents
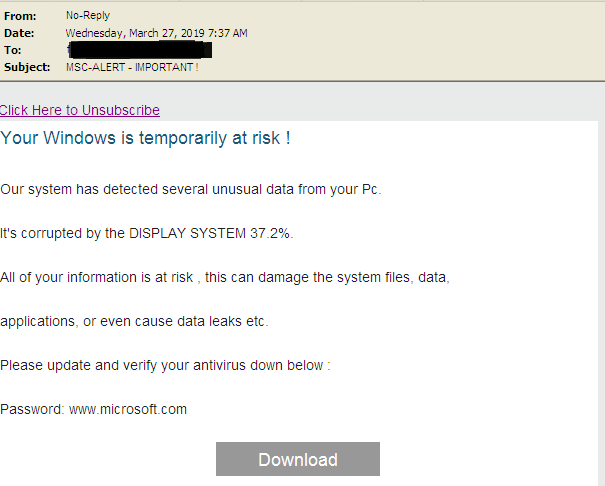
Example of the spam email content:
Your Windows is temporarily at risk!
Our system has detected several unusual data from your PC.
It's corrupted by the DISPLAY SYSTEM 37.2%.
All your information is at risk, this can damage system files, data, applications, or even cause data leaks, etc.
Please update and verify your antivirus down below:
Password: www.microsoft.com
Download
Execution and Distraction
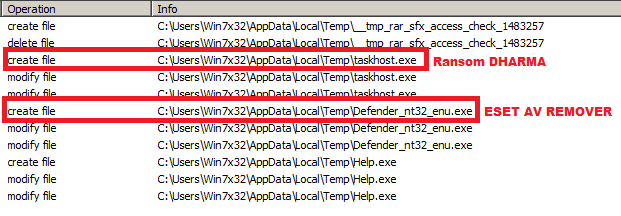
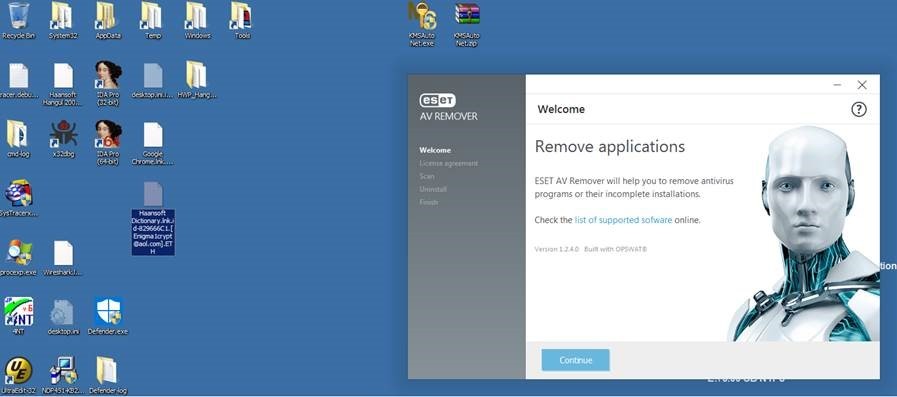
Once executed, Defender.exe drops an old ESET AV Remover installer (Defender_nt32_enu.exe) and a Dharma binary (taskhost.exe) in the Startup folder. The ESET installer launches, distracting the victim, while the Dharma ransomware encrypts the hard drive in the background.
Encryption and Contact Information
Tests show that this campaign installs a Dharma variant that appends the ETH extension to encrypted files. It also uses the Enigma1crypt@aol.com email address for contact.
Trend Micro Analysis
Trend Micro notes, “The ransomware will still encrypt files even if the installation is not started. The malware runs on a different instance than the software installation, so their behaviors are not related.”
ESET Statement
Following Trend Micro’s report, ESET issued a statement: “The article describes the well-known practice of bundling malware with legitimate applications. In this case, an official and unmodified ESET AV Remover was used as a decoy. However, any application could be used this way. This is a distraction technique. ESET engineers have seen several cases of ransomware packed with clean files or hacks/cracks recently.”
Indicators of Compromise (IOCs)
Trend Micro provides a list of IOCs at the end of their report to help detect and block attacks using this Dharma ransomware strain.
Sequence Diagram for Dharma Ransomware Attack Process

Dharma Ransomware Awareness & Decryption | Cyber Security
Dharma Ransomware Uses AV Tool to Hide Activities – Indicators of Compromise
Trend Micro recently found new samples of Dharma ransomware using a new technique: using software installation as a distraction to help hide malicious activities.
The Dharma ransomware has been around since 2016, but it has continued to target and successfully victimize users and organizations around the world. One high profile attack happened in November 2018 when the ransomware infected a hospital in Texas, encrypting many of their stored records; luckily the hospital was able to recover from the attack without paying the ransom. Trend Micro recently found new samples of Dharma ransomware using a new technique: using software installation as a distraction to help hide malicious activities.
Dharma ransomware actors abuse AV tool – Dharma Ransomware Uses Legit Antivirus Tool To Distract Victims
New samples of Dharma ransomware show that it is still being distributed via spam mail. Typical of spam, the message pressures users into downloading a file. If a user clicks on the download link, they will be prompted for a password (provided in the email message) before getting the file.
Figure 1. Dharma ransomware infection chain
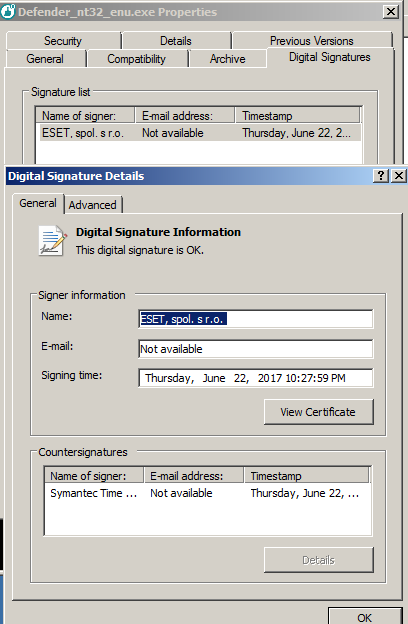
The downloaded file is a self-extracting archive named Defender.exe, which drops the malicious file taskhost.exe as well as the installer of an old version of ESET AV Remover renamed as Defender_nt32_enu.exe. Trend Micro identifies taskhost.exe as a file connected to the Dharma ransomware (detected as RANSOM.WIN32.DHARMA.THDAAAI)
Figure 2. Spam mail for Dharma ransomware
Figure 3. Running the self-extracting archive (Defender.exe)
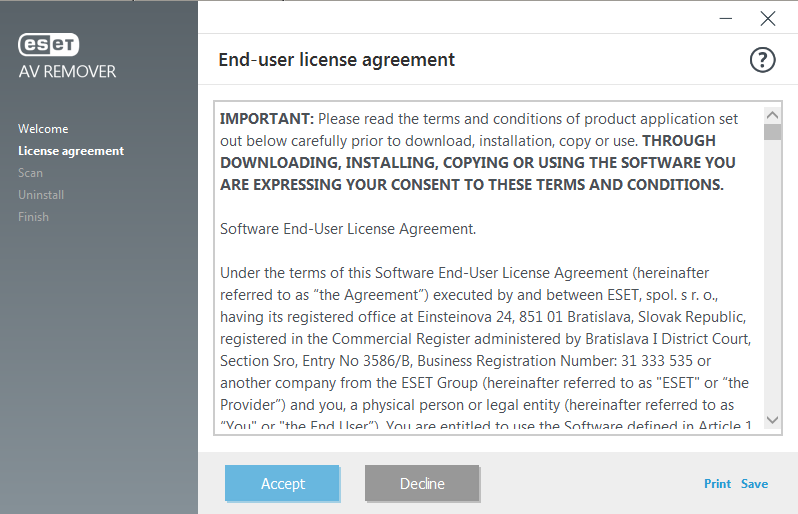
The ransomware uses this old ESET AV Remover installer, which appears unmodified based on initial scanning, to divert attention as it encrypts files on the victim’s device. When the self-extracting archive runs, Dharma starts encrypting files in the background and the ESET AV Remover installation begins. The user will see the ESET GUI onscreen, a distraction from Dharma’s malicious activities.
Figure 4. Software installation distracts from the ransomware’s activities
Figure 5. Software installation runs on a different instance than malware
The AV Remover is a working tool that goes through the familiar installation routine if it is executed. However, the ransomware will still encrypt files even if the installation is not started. The malware runs on a different instance than the software installation, so their behavior is not related.
The tool is legitimate software bundled with the malware, so user interaction is necessary to fully install it. The ransomware will run even if the tool installation is not triggered, and the tool can be installed even if the ransomware does not run. The installation process seems included just to trick users into thinking no malicious activity is going on.
Figure 6. The ESET installer file also has a valid digital signature, so this also helps it stay under the radar
Cybercriminals have a history of abusing authentic tools, and this recent Dharma tactic of using an installer as a diversion or screen of legitimacy is simply another method they are experimenting with. This new version is designed to trick users and allow the ransomware to stealthily operate in the background. As malware authors continue to adopt layered evasion tactics and malicious techniques, users also have to adopt stronger and smarter security solutions to protect their assets.
ESET was informed of this research before publishing and issued this response:
The article describes the well-known practice for malware to be bundled with legitimate application(s). In the specific case Trend Micro is documenting, an official and unmodified ESET AV Remover was used. However, any other application could be used this way. The main reason is to distract the user, this application is used as a decoy application. ESET threat detection engineers have seen several cases of ransomware packed in self-extract package together with some clean files or hack/keygen/crack recently. So this is nothing new.
In the specific case described by Trend Micro, the ransomware is executed right after our remover application, but the remover has a dialogue and waits for user interaction, so there is no chance to remove any AV solution before the ransomware is fully executed.
How to defend against ransomware – Dharma Ransomware Uses Legit Antivirus Tool To Distract Victims
There has been a growing awareness about ransomware as well as improved solutions for organizations and users, which contributes to ransomware’s continuing decline. However, as proven by the new samples of Dharma, many malicious actors are still trying to upgrade old threats and use new techniques. Ransomware remains a costly and versatile threat; earlier this month a ransomware family was spotted targeting vulnerable Samba servers. This particular ransomware first emerged as a threat targeting victim’s network-attached storage device before it evolved to target other devices.
Users and organizations should prepare for Dharma and similar threats by adopting good cybersecurity hygiene. Some best practices to follow include:
- Secure email gateways to thwart threats via spam and avoid opening suspicious emails.
- Regularly back up files.
- Keep systems and applications updated, or use virtual patching for legacy or unpatchable systems and software.
- Enforce the principle of least privilege: Secure system administrations tools that attackers could abuse; implement network segmentation and data categorization to minimize further exposure of mission-critical and sensitive data; and disable third-party or outdated components that could be used as entry points.
- Implement defense in depth: Additional layers of security like application control and behavior monitoring helps thwart unwanted modifications to the system or execution of anomalous files.
- Foster a culture of security in the workplace
Indicators of Compromise – Dharma Ransomware Uses Legit Antivirus Tool To Distract Victims
| File Name | SHA256 | Detection |
| Defender.exe | a5de5b0e2a1da6e958955c189db72467ec0f8daaa9f9f5ccc44e71c6c5d8add4 | Ransom.Win32.DHARMA.THDAAAI |
| taskhost.exe1 | 703b57adaf02eef74097e5de9d0bbd06fc2c29ea7f92c90d54a0b9a01172babe | Ransom.Win32.DHARMA.THDAAAI |
| Defender_nt32_enu.exe1 | 0d7e4d980ae644438ee17c1ea61ac076983ec3efb3cc9d3b588d2d92e52d7c83 | normal ESET AV remover |
| packager.dll | 083b92a07beebbd9c7d089648b1949f78929410464578a36713033bbd3a8ecea | normal |
| panmap.dll | 9ada26a385e8b10f76b7c4f05d591b282bd42e7f429c7bbe7ef0bb0d6499d729 | normal |
| sspisrv.dll | f195983cdf8256f1d1425cc7683f9bf5c624928339ddb4e3da96fdae2657813d | normal |
| sstpsvc.dll | 39d3254383e3f49fd3e2dff8212f4b5744d8d5e0a6bb320516c5ee525ad211eb | normal |
Related Videos:
Related Posts:
Comprehensive Guide to Malware Removal: Steps and Resources for Securing Your PC
DIY Guide: Building Your Own Raspberry Pi Media Center
Fake Google reCAPTCHA used to hide Android banking malware
Network Security Hacks 2nd Edition
Network Security Hacks 2nd Edition
Context in Outbound Links for High Ranking SEO
What is Healthcare Cybersecurity in organizations?